Some links on this page are affiliate links. We may earn a commission when you click through and make a purchase, at no additional cost to you.
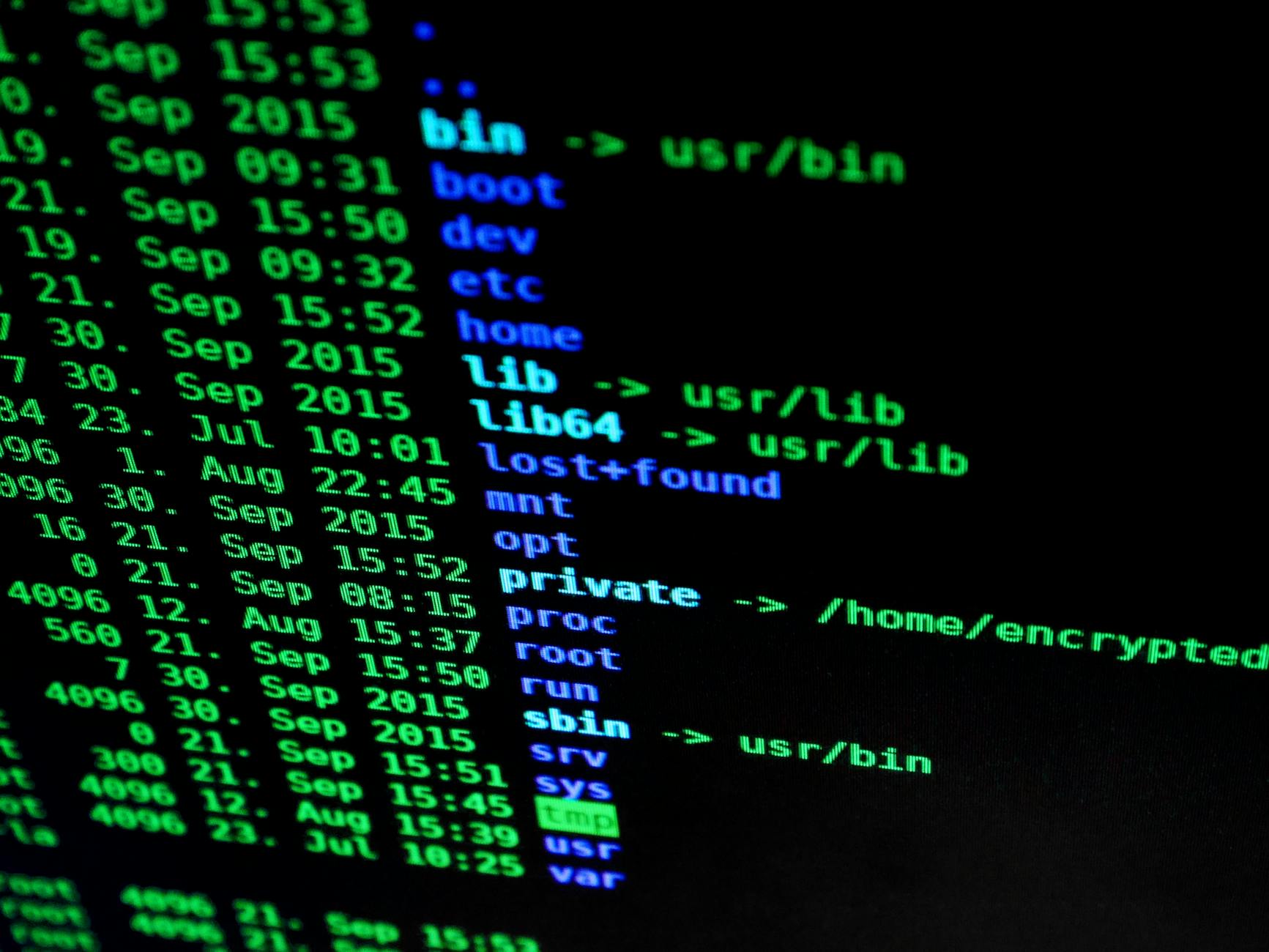
Wordfence’s latest report shines a light on the security landscape of the WordPress ecosystem, revealing 204 vulnerabilities across 77 plugins and 119 themes. This comprehensive Wordfence Intelligence report underscores the critical need for site operators to stay vigilant and proactive.
The sheer volume of vulnerabilities disclosed last week highlights the ongoing challenges in maintaining secure WordPress environments. Among the vulnerabilities, 131 were rated as high severity, with three deemed critical. These findings are crucial for developers, security professionals, and site owners who rely on WordPress’s ecosystem.
Triple Threat Bug Bounty Challenge
Wordfence has launched a significant initiative to encourage the discovery and reporting of high threat vulnerabilities. The ‘Triple Threat Bug Bounty Challenge’ offers triple incentives for vulnerabilities classified as high threat. Researchers can earn 2x the standard bounty for these vulnerabilities, with an additional 30% bonus for those affecting software with over 30,000 active installs, excluding those with over 5 million installs. Furthermore, an extra $300 is awarded for every three high threat vulnerabilities reported, provided they affect software with at least 1,000 installs.
This challenge not only incentivizes the discovery of vulnerabilities but also enhances the overall security posture of the WordPress ecosystem by encouraging thorough scrutiny of widely-used plugins and themes.
New Firewall Rules and Protection Measures
In response to the identified vulnerabilities, the Wordfence Threat Intelligence Team has deployed new firewall rules to bolster protection for its Premium, Care, and Response customers. Notably, vulnerabilities in ‘Master Addons for Elementor Premium’ and ‘WooCommerce Wholesale Lead Capture’ have been addressed with new rules to mitigate risks such as authenticated remote code execution and unauthenticated privilege escalation.
These measures ensure that premium users receive immediate protection, while users of the free Wordfence version will benefit from these enhancements after a 30-day delay. This proactive approach demonstrates Wordfence’s commitment to delivering timely security updates to its user base.
Vulnerability Breakdown and Impact
The report categorizes vulnerabilities by severity and type, providing a granular view of the WordPress security landscape. Improper control of filenames for include/require statements in PHP programs tops the list with 99 occurrences, followed by 43 instances of cross-site scripting vulnerabilities. These figures highlight the persistent nature of common vulnerabilities within the WordPress ecosystem.
With 41 vulnerabilities patched and 163 remaining unpatched, the report underscores the critical need for developers and site operators to prioritize patch management and vulnerability remediation. The availability of Wordfence’s free tools, such as the CLI Vulnerability Scanner and the vulnerability database API, equips users with the resources needed to implement effective security measures.
What To Do
- Developers: Regularly review and apply patches for your plugins and themes. Engage with bug bounty programs to identify vulnerabilities.
- Site Operators: Utilize Wordfence’s CLI Vulnerability Scanner for regular scans. Subscribe to vulnerability databases to stay informed.
- Security Professionals: Monitor vulnerability disclosures and firewall updates through Wordfence’s API and webhook integrations.